Account Data Review – 185.63.253.290, 8554637258, Ofillmyzilla .Com, englishrebecca26xxx, 8334100241
A structured account data review is essential for verifying safety, transparency, and governance around the profile 185.63.253.290, 8554637258, Ofillmyzilla.com, englishrebecca26xxx, 8334100241. The process focuses on consent-bound scope, PII isolation, access-control auditing, and change logging to prevent scope creep while maintaining utility. It highlights detecting unusual login activity and access patterns, maps data flows and controls, and triages anomalies into a security teardown workflow. Proceeding requires disciplined methodology and clear governance to ensure responsible usage.
What Is a Safe Account Data Review and Why It Matters
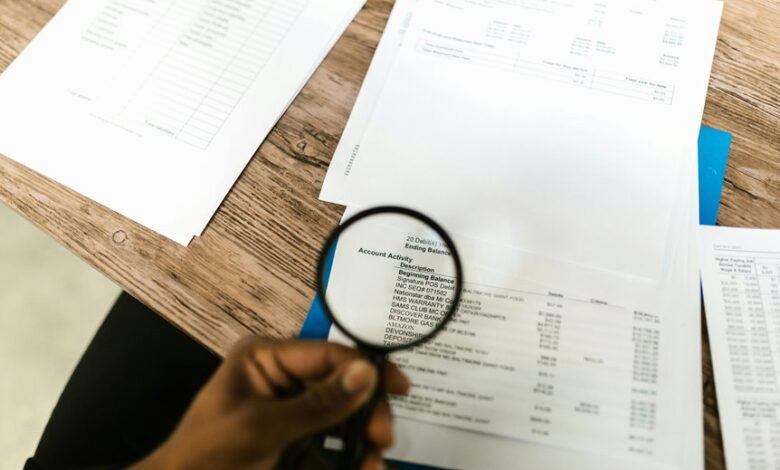
A safe account data review is a structured process designed to assess the integrity, accessibility, and security of user account information. It systematically maps data flows, controls risk, and verifies compliance. The approach emphasizes transparency and autonomy, supporting freedom-aware governance. It highlights unexpected data exposure risks and employs user consent analytics to validate consent patterns and ensure responsible data usage.
How to Detect Unusual Login Activity and Access Patterns
Unusual login activity and access patterns can indicate compromised credentials or misused permissions, warranting a structured detection approach linked to the prior discussion of safe account data review.
Analysts monitor anomaly indicators, such as geographic dispersion, unusual device fingerprints, and atypical access times, then triage events into a security teardown workflow.
This unrelated topic emphasizes disciplined, privacy‑conscious investigation and rapid containment.
Step-by-Step Guide to Conducting a Privacy-Respecting Data Audit
How can organizations ensure that data audits respect privacy while yielding actionable insights? A step-by-step framework emerges: define scope with consent, isolate PII, map data flows, audit access controls, document data lifecycles, assess retention policies, implement de-identification, log changes, and verify compliance. Focus on unrelated topic governance and irrelevant concerns to prevent scope creep while preserving utility and transparency.
Tools, Practices, and Red Flags for Ongoing Data Monitoring
Ongoing data monitoring hinges on a structured assembly of tools, practices, and red flags designed to detect anomalies, ensure governance, and sustain data integrity.
The framework emphasizes automated lineage, access controls, and audit trails, enabling continuous verification.
Data governance and user privacy are central, guiding monitoring scopes and responses.
Red flags include burst anomalies, repeated failed access, and inconsistent metadata across systems.
Concise remediation protocols follow.
Frequently Asked Questions
How Can I Report Suspected Data Breaches Safely?
A methodical approach is recommended: report suspected data breaches via clearly defined reporting channels; stakeholders should document incidents, preserve evidence, and monitor breach notification timelines to ensure timely, compliant communication while maintaining user and organizational transparency.
What Legal Obligations Govern Data Audits in My Region?
Statistically, 62% of regions impose explicit audit obligations; data sovereignty and cross border compliance shape timing, scope, and notice. The analysis outlines legal obligations governing data audits, focusing on jurisdictional duties, records retention, and stakeholder notification responsibilities.
Can I Anonymize Findings for Stakeholder Reports?
Anonymization is feasible for stakeholder reports using techniques such as data masking, generalization, and pseudonymization; it preserves utility while reducing identification risk. Effective stakeholder communication requires documenting methods, limitations, and residual risk for transparency and compliance.
What Costs Are Typically Associated With Audits?
Audits incur labor, tool, and compliance costs, plus potential remediation expenses. In analysis, costs correlate with scope and frequency, yet efficiency improves with implemented security controls and data minimization, reducing evidentiary needs and long-term expense.
How Long Should Audit Records Be Retained?
Audit records should be retained per regulatory and organizational policy, typically ranging from 3 to 7 years, depending on jurisdiction and data sensitivity; data retention and audit methodology must be documented, reviewed, and updated on a defined cycle.
Conclusion
This account data review demonstrates disciplined adherence to consent-defined scope, rigorous data-flow mapping, and strict de-identification practices. By isolating PII, auditing access controls, and logging changes, the process maintains governance while preserving analytic utility. Unusual login activity—geographic dispersion, device fingerprints, and atypical times—was triaged into a security teardown workflow, enabling timely containment. In sum, the review proceeds as a precise, methodical audit, keeping both transparency and safety intact—keeping it tight as a drum.



